Non-technical people find it difficult to understand cryptography or to choose encryption methods for securing their sensitive data. They don’t have a fair idea about encryption, its types, how one differs from the other, and which one is ideal for their organization.
This article is solely for those non-techies whose minds are jumbled between which encryption to choose and why. This article may also help some techies widen their knowledge on encryption, its functioning, types, and differences.
Let’s plummet into the encryption security pool to check out some basics.
An Overview: What Is Encryption?
When communication is made between the browser and the server, it is in a plain format. But to keep it secured from hackers, the same is converted into a ciphertext (gibberish language) which is difficult to read. This process of conversion of plain text into ciphertext is called encryption. This conversion is done with the help of encryption algorithms and keys.
Encryption is becoming a pivotal part of the digital business. Encryption is essential in e-mail communications for securing data in the healthcare industry, online shopping, the insurance sector, etc., to protect against cyber-attacks.
There are two types of encryptions:
- Symmetric Encryption
- Asymmetric Encryption
Both these encryption types have their similarities and differences. Let’s explore each of them individually to find out which one surpasses the other.
Symmetric Encryption:
In Symmetric encryption, only one key is used for encrypting and decrypting the messages. Here the whole process is handled with one secret key.
Encryption algorithms (block ciphers or stream ciphers), including the private key, helps in converting the plain text into ciphertext, and the same key will be used to convert the ciphertext into plain text.
Only the intended recipient has the key for decrypting the message. The secret key looks gibberish because it combines random string, letters, numerals, or words. Adequate security needs to be maintained while sharing the secret key to prevent it from being compromised.
Since symmetric encryption involves two parties and one shared key, both parties are aware of the secret key for encrypting or decrypting the message.
Examples: Blowfish, AES, RC5, etc., of which AES-128 and AES-192 are some popular names
Pros:
- It functions faster since only one private key is used in the process.
- It works best to store data at external places like hard drives, USB, flash drives, etc.
- It’s an old, easy and simple process
Cons:
- The entire process of encoding or decoding the information requires only one key, so if the same is compromised or stolen, the intruder can intercept the message and misuse it.
Asymmetric Encryption:
Asymmetric encryption (public-key cryptography) requires two separate key pairs linked to each other with mathematical algorithms for encrypting or decrypting the information. The key pairs are named public keys and private keys.
The public key encrypts the text, and hence it is used by many people, whereas the private key lies with the intended recipient only. Only the private key owner can decrypt the message. In short, the public key is used for the encryption of text, whereas the private key is used for the decryption of text.
Examples: Diffie-Hellman, RSA, DSA, ECC, etc. are some common names
Pros:
- Security in asymmetric encryption is stronger since the private key is never shared.
- This encryption is more secure because even if one key is stolen, the intruder cannot access the information without gaining the other key.
- This encryption is generally used in digital signatures and digital documents, where robust security is essential.
- It gives better scalability.
Cons:
- Asymmetric encryption is a complex and complicated process.
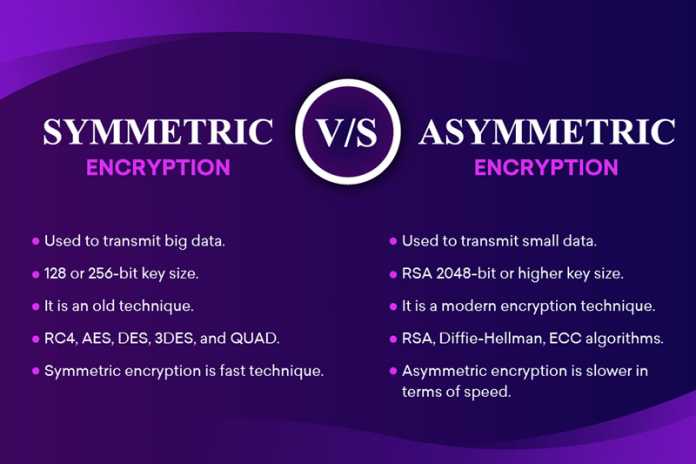
Symmetric Vs Asymmetric Encryption
| Comparison Criteria | Symmetric Encryption | Asymmetric Encryption |
| 1. Symmetric Keys Vs. Asymmetric Keys | A single key, i.e., a secret key, is used in the encryption and decryption process. This secret key encrypts and decrypts messages. | Two different keys, i.e., a public key and a private key, are used in the encryption and decryption process. The public key encrypts, whereas the private key decrypts the same. |
| 2. The Main Aim | Fast execution and easy process make symmetric encryption ideal in data transmission from storage to external devices. | Asymmetric encryption is the best viable option for those with daily data transmissions and those who prefer a secured environment. |
| 3. The factor of Ease and Simplicity | The use of only one key in the entire process makes the process simple and easy. | The use of 2 keys in the process makes the process complex. |
| 4. Name | This encryption is named private-key cryptography. | This encryption is named public-key cryptography. |
| 5. Performance Analysis | The process is performed very quickly. | The process takes a long time because the keys need to be matched and compared. |
| 6. Algorithms Used | Symmetric encryption works on the below-mentioned algorithms:
|
Asymmetric encryption works on the below-mentioned algorithms:
|
| 7. Key Length | The key length used in symmetric encryption varies between 128-bits or 256-bits. | The key length used in asymmetric encryption is 2048-bits or high. |
| 8. Security Quotient | Sharing of secret keys increases the risk of it being compromised. | Since the pair of keys are not to be shared, the risk of the key being compromised is very less. |
| 9. Technology | This is an old encryption technique. | This is a new encryption technique. |
| 10. Size of Cipher Text | The ciphertext which is created is smaller than the plain text. | The ciphertext which is created is larger than the plain text. |
| 11. Utilization of Resources | Very few resources are utilized in symmetric encryption. | Vast resources are utilized in asymmetric encryption. |
| 12. Benefits | This encryption provides confidentiality. | This encryption provides data privacy, authenticity, and data integrity. |
Which One is Better?
The answer to the question solely depends on the security needs and situations. As said previously in the article, data transmissions from storage to external devices are best done with symmetric encryption. But when small data transfers and daily transactions are done, asymmetric encryption is more secure.
WhatsApp and most messaging applications use asymmetric encryption to safeguard the message, whereas asymmetric encryption for initiating secured encrypted conversations.
Even HTTPS (hyper-text transfer protocol secure) connections (where SSL certificate is installed) use both these encryptions to secure website data and information.
If you are website owner, you must buy SSL certificate for your website’s security. There are many SSL brands available in market like Comodo SSL certificate, RapidSSL Certificate, GeoTrust, GlobalSign, Thawte, DigiCert and more. I have found one SSL provider, Cheapsslshop.com who offers huge discount on SSL certificates with great customer support. You can choose any certificate as per your website’s requirement.
In a Nutshell:
There are pros and cons to both types of encryptions. That is the sole reason why they both connect to give incredible digital security. Considering the latest technology and digital security, asymmetric encryption is more reliable than symmetric encryption.
There are numerous cases where symmetric encryption is used, specifically in bulk transmissions. So, when we check out the digital securities and technology factors, both play an equal role in digital security because one without the other is incomplete. The internet is a risky place, and hence both these encryption securities are crucial for securing the same.